A Practical Guide for Businesses and Organizations
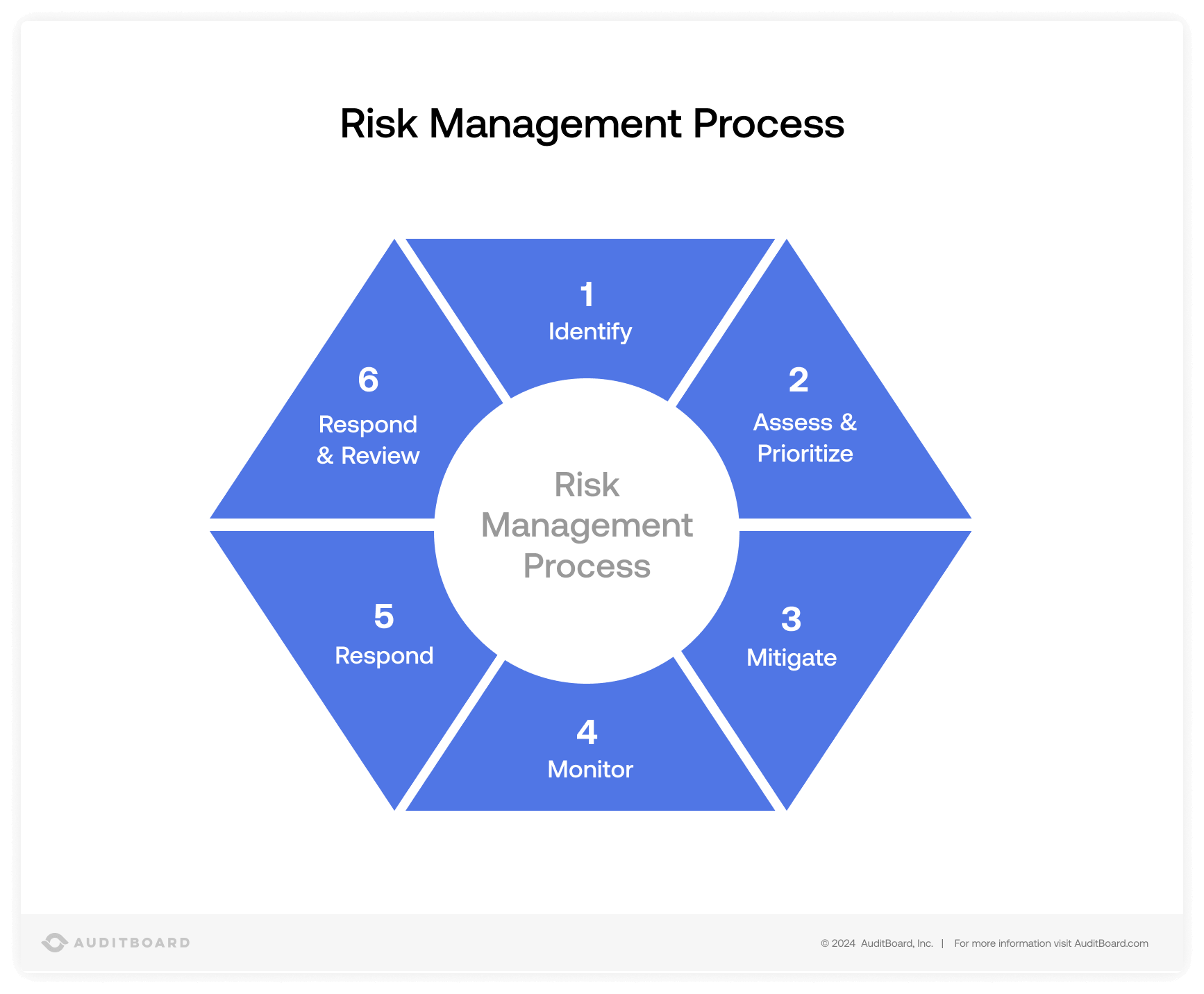
In today’s fast-moving digital and physical environment, risk is everywhere — from cyber threats and internal fraud to physical breaches and operational disruptions. Effective risk monitoring and security management ensures that threats are identified early and handled before they cause serious damage.
This guide explains how to manage risk monitoring security step-by-step, whether you run a small business, corporate firm, or security-focused organization.
1. Understand What Risk Monitoring Means
Risk monitoring is the continuous process of:
-
Identifying threats
-
Assessing vulnerabilities
-
Tracking suspicious activity
-
Preventing potential damage
It combines security systems, human intelligence, and strategic planning to protect assets, people, and data.
2. Identify Potential Risks
The first step is risk identification. Risks can be categorized into:
🔐 Physical Risks
-
Unauthorized access
-
Theft or vandalism
-
Workplace violence
💻 Cyber Risks
-
Data breaches
-
Malware attacks
-
Phishing scams
📊 Operational Risks
-
Employee misconduct
-
Fraud
-
Process failures
Professional security firms and investigative agencies often conduct formal risk assessments to document vulnerabilities before designing a monitoring system.
3. Conduct a Risk Assessment
A proper assessment includes:
-
Evaluating physical entry points
-
Reviewing surveillance coverage
-
Checking cybersecurity protocols
-
Analyzing internal processes
-
Identifying high-value assets
The goal is to determine likelihood vs. impact for each potential threat.
4. Implement Security Controls
Once risks are identified, implement layered protection systems:
Physical Security Measures
-
CCTV monitoring
-
Access control systems
-
Alarm systems
-
Security personnel
Cybersecurity Controls
-
Firewalls
-
Encrypted networks
-
Two-factor authentication
-
Regular software updates
Administrative Controls
-
Employee background checks
-
Clear security policies
-
Incident reporting systems
A multi-layered approach significantly reduces vulnerability.
5. Continuous Monitoring & Surveillance
Risk monitoring is not a one-time task — it requires constant observation.
Effective monitoring includes:
-
24/7 CCTV surveillance
-
Real-time system alerts
-
Log analysis
-
Behavioral monitoring
-
Incident response tracking
Modern organizations use Security Operations Centers (SOC) for centralized monitoring.
6. Incident Response Planning
No system is 100% risk-free. That’s why an incident response plan is critical.
A good response plan includes:
-
Clear reporting structure
-
Immediate containment procedures
-
Evidence preservation
-
Communication protocol
-
Post-incident review
Quick response reduces financial and reputational damage.
7. Regular Audits & Updates
Security threats evolve constantly. To stay protected:
-
Conduct quarterly audits
-
Test surveillance systems
-
Update software
-
Re-train staff
-
Review access privileges
Proactive updates prevent outdated systems from becoming vulnerabilities.
8. Role of Professional Security & Investigation Firms
Many organizations hire licensed private investigators or security consultants to:
-
Conduct undercover risk audits
-
Monitor internal fraud
-
Perform background investigations
-
Provide surveillance services
-
Ensure compliance with legal standards
External experts offer objective analysis and specialized tools that internal teams may lack.
9. Key Principles of Effective Risk Monitoring
✔ Prevention over reaction
✔ Continuous vigilance
✔ Legal compliance
✔ Documentation of all activities
✔ Clear accountability
Strong risk monitoring creates confidence, stability, and long-term protection.
Final Thoughts
Managing risk monitoring security is not just about cameras or alarms — it’s about building a system that detects threats early, responds quickly, and continuously adapts to new challenges.
Whether protecting sensitive data, physical property, or corporate reputation, structured risk monitoring ensures your organization stays secure in an unpredictable world.
Security is not an expense — it’s an investment in stability and protection.










Leave A Comment